February 2015

Who Else Wants To Win A $25 Gift Card?

Now, here’s this month’s trivia question. The winner will receive a $25 Gift Card.
Which country consumes the most chocolate per person at 26 lbs. or 11.9 kg per year?
A) Belgium B) Switzerland C) Germany D) Brazil
Call us right now with your answer!
*Trivia winners are eligible to win again after 90 days of previous win.
Are You Making These 3 Common And Costly Mistakes
With Your Online Data Backups?
Offsite backups have been touted in the past few years as the answer to everyone’s bad habit of not doing backups. Once signed up for an online service it’s easy to ‘set it and forget it;’ but too many business owners don’t know what they are buying and end up paying a lot more than they should. They also end up shocked when they discover they weren’t backing up the right files or that they can’t restore the files as quickly as they had hoped.
If you want to make sure you don’t get burned by your online backup, avoid these 3 common mistakes:
Mistake #1: Not choosing an online backup service that offers a file versioning feature. In the old days of tape backups when a proper tape rotation was used, it would be possible to go back to a specific version of a file from different time periods. In other words it was possible to restore a spreadsheet you worked on last night and three weeks ago.
Most online backup services only back up the last version of a file; so make sure you choose one that features file versioning and configure it for 60-90 days of versioning on files that are frequently used.
Mistake #2: Backing up everything. In most cases, only data files need to be backed up. Some business owners accidently select their whole server and/or computer when beginning the process and end up paying to back up files and programs that do not need to be copied. This can lead to exponentially higher monthly charges with no added benefit. It’s often best to have a professional help you set up your backup criteria the first time to make sure you’re not missing files or data that might be buried a few levels deep—or backing up unnecessary files.
Mistake #3: Not having a local backup. Online backup services are great as a daily backup and eliminate the headache of changing tapes, disks, etc. However, if you only have an online backup, it can take a few hours to a few days to fully download your data back onto your server. That’s why it’s always a good idea to have a current local backup. Aside from being able to retrieve data a lot more quickly from your local backup, it can make the process of rebuilding an entire system a lot faster and less painful.
Want To Get A 100% Rock-Solid Backup Of Your Data
To Ensure A Fast, Painless Recovery Of Your Data?
Call us now: 214-329-1349. You’ll sleep easier at night
AND save yourself a TON of cash, guaranteed!
How To Keep Your Laptop Secure
When Using Public WiFi Hotspots
They are everywhere these days. WiFi hotspots for checking e-mail and hopping on the Internet can be found in airports, coffee shops and even most fast-food joints. But have you ever wondered, just how safe is it to connect? With the proliferation of hackers, viruses and identity theft at an all-time high, you are smart to be concerned. Unfortunately, it is easy for a hacker to set up a WiFi spot to access your laptop, called an “evil twin.” An evil twin is a wireless hotspot that is used to lure people from a nearby, legitimate hotspot. For example, when logging in at your favorite coffee shop, you may have inadvertently logged in to an evil twin Internet connection set up by the person working on a laptop at the next table.
Just like legitimate sites, evil twins allow you access to the Internet, but in the background they record everything you are typing. Log on to your e-mail, investment web site or bank account, or buy something online, and they are recording your keystrokes.
Tip: Do you want an easy way to securely access your network and the Internet from anywhere? Call us today at about setting up a VPN for your office!
You may be asking, “How do I protect myself at WiFi hotspots?” First you need to make sure the hotspot is legitimate. You can do this by asking someone who works at the WiFi location; in fact, some businesses will give you printed instructions that include the hotspot name. Even here you need to be careful. Many times, in an attempt to make you feel comfortable, the hacker will use an evil twin name that mimics the legitimate hotspot and, on some occasions, the fake site may even show up at the top of your network list by having a stronger signal than the legitimate site.
The best protection you can have is connecting via your company’s VPN (virtual private network).
A VPN protects your online information by encrypting your data and activity even if you’re connected through an evil twin. If you don’t have a VPN, the best protection is to surf the net, but never type in password, credit card, social security, bank account or other sensitive information when connected to a public WiFi hotspot.
VIRUS OF THE MONTH: Anonymizing Proxy
Anonymizing proxies allow the user to hide their web browsing activity. They are often used to bypass web security filters—e.g., to access blocked sites from a work computer.
Anonymizing proxies hold significant risks for organizations:
Liability: Organizations can be legally liable if their computers are used to view pornography, hate material or to incite illegal behavior. There are also ramifications if users violate third-party licenses through illegal MP3, film and software downloads
Productivity: Anonymizing proxies can permit users to visit sites that, although safe, are often used for non-work purposes”
- “Anonymizing Proxy.” Threatsaurus: the a-z of computer and data security threats.. Boston: Sophos, 2009. 11. Print.

How To Grow Star Performers
A study of computer programmers at Bell Laboratories showed that the star performers outperformed moderate performers by a margin of 8 to 1. If that holds true in your organization, the conversion of five of your moderate performers into star performers would be the equivalent of adding 35 moderate performers to your workforce. Where are you going to find the five additional star performers? You don’t find them. You develop them.
A study of computer programmers at Bell Laboratories showed that the star performers outperformed moderate performers by a margin of 8 to 1. If that holds true in your organization, the conversion of five of your moderate performers into star performers would be the equivalent of adding 35 moderate performers to your workforce. Where are you going to find the five additional star performers? You don’t find them. You develop them.
- Taking initiative: accepting responsibility above and beyond your stated job, volunteering for additional activities and promoting new ideas.
- Networking: getting direct and immediate access to coworkers with technical expertise and sharing your own knowledge with those who need it.
- Self-management: regulating your own work commitments, time, performance level and career growth.
- Teamwork effectiveness: assuming joint responsibility for work activities, coordinating efforts and accomplishing shared goals with workers.
- Leadership: formulating, stating and building consensus on common goals and working to accomplish them.
- Followership: helping the leader to accomplish the organization’s goals and thinking for yourself rather than relying solely on managerial direction.
- Perspective: seeing your job in its larger context and taking on other viewpoints, like those of the customer, manager and work team.
- Show-and-tell: presenting your ideas persuasively in written or oral form.
- Organizational savvy: navigating the competing interests in an organization, be they individual or group, to promote cooperation, address conflicts and get things done.
Star performers considered initiative, technical competence and other cognitive abilities to be core competencies. Show-and-tell and organizational savvy were on the outer edge of their circle of importance. Middle performers placed show-and-tell and organizational savvy at the center. While star performers were focused on performance, middle performers were focused on impressing management.
Star performers and middle performers also showed marked differences in their attitudes toward networking. The middle performers waited until after they had encountered problems before looking around for someone who could provide help and support. The star performers built a network of helpers and supporters in advance, so they could call on them immediately when needed.
The study concluded that “Individual productivity… depends on the ability to channel one’s expertise, creativity and insight into working with other professionals.”
Star performers emerge from educational systems tailored to the individual company and the individual job. They don’t want to become clones. Too many companies today are content with training programs that provide people with knowledge and expertise, but skimp on educational processes that teach them to apply what they learn. You can’t train them to seek excellence. You change that attitude through consistent input that appeals to an individual’s self-interest and organizational spirit.

Foundation in Arizona.
Dr. Nido Qubein is president of High Point University, an undergraduate and graduate institution with 4,300 students from 40 countries. He has authored two dozen books and audio programs distributed worldwide. As a business leader, he is chairman of the Great Harvest Bread Company, with 220 stores in 43 states. He serves on the boards of several national organizations, including BB&T (a Fortune 500 company with $185 billion in assets), the La-Z-Boy Corporation (one of the largest and most recognized furniture brands worldwide) and Dots Stores (a chain of fashion boutiques with more than 400 locations across the country). As a professional speaker, Dr. Qubein has received many distinctions, including the Golden Gavel Medal, induction into the International Speaker Hall of Fame and as the founder of the NSA
To learn more about Dr. Qubein, go to: http://www.nidoqubein.com/
Shiny New Gadget Of The Month: Prizm

This month’s gadget is so new, it isn’t even off the assembly line. Meet Prizm — a small, pyramid-shaped device designed to make your home-audio experience as hands-off as humanly possible. The device was recently backed on Kickstarter this past November. The French company behind the audio device wanted to create an intuitive music experience that brings users new music, while learning what they really love to listen to.
The device streams music from cloud services such as Deezer, Spotify and SoundCloud, with more services planned in the future. It works by accessing your WiFi network. It doesn’t contain any speakers, so you’ll have to supply your own (it connects via Bluetooth, 3.5 mm stereo jack and optical audio). And despite being called hands-off, the device sports buttons to let you like or skip songs to customize your listening experience.
It can currently be pre-ordered from www.meetprizm.com for $139
Protect Yourself from Online Credit Card Fraud
The past couple of years have been a rough ride for anyone who relies on a credit card to make purchases. Data breaches have plagued retail stores in the U.S. and Canada. Credit card providers are set to roll out new, more secure credit cards to consumers this year, catching up to Europe and much of Asia in terms of credit card security. The U.S., in particular, has lagged behind in credit card security due in part to the cost of upgrading both the cards themselves and the pay terminals.
If you are concerned about your credit card information falling into the wrong hands, there are several steps you can take to protect yourself:
Only give your credit card information to secure and trusted web sites. Never enter any personal or financial information on a non-secure web page. If you don’t see “https” in the web address, move along.
Monitor all activity. Regularly check your credit card and bank statements. The simplest way to spot fraud is to monitor all your financial activity. Many credit card providers have custom alerts you can set to notify you if certain purchases are made.
Never save credit card information. Many online retailers and shops now ask if you would like to save your credit card information for future use. While it may seem convenient, skip it.
Delete your cookies and auto-fill data. When you enter information on a web page, that data is stored in your web browser. After you complete a transaction, go into your browser’s options, settings or history tab and delete the data.
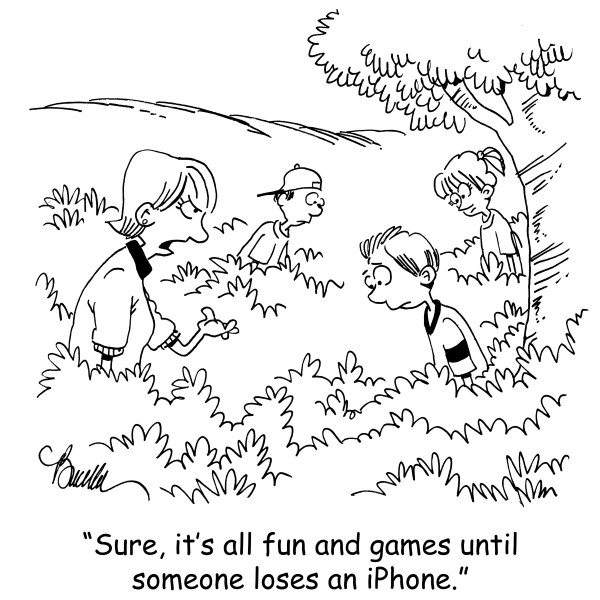
The Lighter Side:
Punch a Painting, Go to Jail
n 2012, Andrew Shannon punched a Monet painting valued at $10 million. The incident occurred at the National Gallery of Ireland, located in Dublin. The painting, entitled Argenteuil Basin with a Single Sailboat, painted in 1874, apparently represented something much greater to the man who decided to attack it.
Right after his initial arrest, Shannon said the attack represented his way of “getting back at the state.” Later on, when he appeared in court, he changed his tune. Instead of an “attack against the state,” he said the whole thing was just a big misunderstanding. He said he didn’t punch the painting, he “fell into it.” He told the court he had felt faint and fell. The painting just happened to be in his way.
Fortunately, the National Gallery has plenty of CCTV cameras and the whole thing was recorded. What did those cameras see? Andrew Shannon very deliberately thrusting his fist through the Monet painting. In December of 2014, he was sentenced to five years in prison, and Argenteuil Basin with a Single Sailboat is back on display after being fully restored.




