December 2014

Trivia Contest
Who Else Wants To Win A $50 Gift Card?

The Grand Prize Winner of last month’s Trivia Challenge Quiz is Lynn Gravley from NT Logistics! He was the first person to correctly answer my quiz question from last month: What two Dallas Cowboys players shared the Most Valuable Player Honor for Super Bowl XII? The correct answer was B) Harvey Martin & Randy White.
Now, here’s this month’s trivia question. The winner will receive a $50 Gift Card.
In Frank Capra’s “It’s a Wonderful Life”, Which financial institution does Mr. Potter take advantage of?
A) New York Private Bank & Trust Corp
B) Bank of Montreal
C) Bailey Bros. Building & Loan
Call us right now with your answer!
*Trivia winners are eligible to win again after 90 days of previous win.
Your Company’s Hidden Security Weakness:
Your Home Wireless Network
As a business owner who also spends time working from home, do you make assumptions about your home’s wireless network security? Between your home and business, chances are your home wireless security is lacking. This can prove to be a serious liability.
WiFi security at home tends to be more lax. It isn’t something business owners worry about. You feel safe at home and you might assume since your business’s network is locked down tight, your data is secure. When an intruder wants to access your business’s proprietary information, they’re going to search for the easiest point of entry.
That is often the home. Intruders are looking for information they can profit from, including financial and identity-related documents. The fact is, there are people who roam around searching for unprotected or poorly protected wireless access.
Never assume your data—personal or business—isn’t accessible. You may inadvertently share critical data without realizing it. You may share files among colleagues and employees and simply forget to turn off sharing permissions. You may place documents and files in a publicly accessible folder. Data-sharing is convenient when you need it, but a liability when it’s readily accessible.
What can you do to protect yourself and your company assets?
- Be aware of when you’re sharing data. If you have any files in a public folder, move them to a more secure location.
- Use a strong password for all your wireless networks. A string of letters, numbers and symbols about 14 characters long is ideal.
- Use WPA2 security. Make sure your router is set up correctly. If you are using WEP or WPA security, change it as soon as possible.
- Change your network's name (SSID). Routers include a default name, and keeping the default tells potential intruders lax security measures may be in place.
And ask yourself how protected your network
and your data—really is.
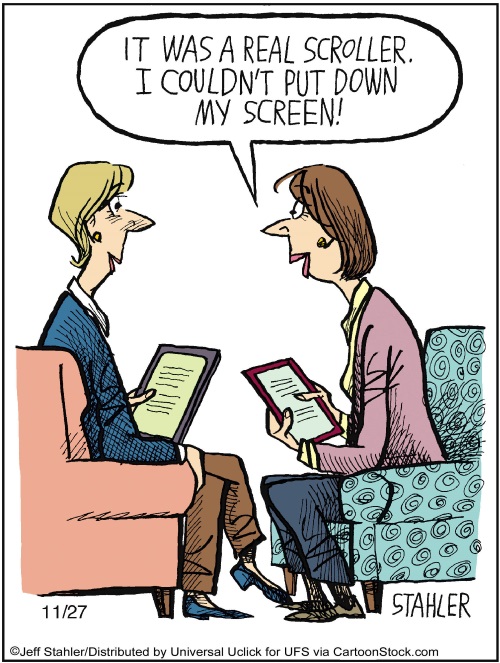
Reducing Distractions in the Workplace
Distractions are everywhere. Our phones, our computers, our tablets, our co-workers, and on and on. When we’re trying to get work done, there is always something, and it’s getting worse. We’re more connected to the Internet than ever before, and there is always one more thing we want to check. It’s safe to blame technology for this constant distraction, but we do need to step up and take a little responsibility for ourselves.
It’s tempting to give in to distraction and let your mind wander for a few minutes, but a few minutes can easily slip into 20 minutes, then 30 minutes, and before you know it, you’re through the first page of Reddit and you’ve filled your quota of cat pictures for the day. There’s nothing wrong with a distraction every once in a while, but when deadlines loom and projects need to get done, it can do more harm than good.
And that doesn’t mean missing your deadlines. The more distracted we become, the more stressed out we become. The deadlines aren’t going to go away, and the more distracted you are, the less time you’ll have to work. Productivity is lost.
What can you do to get productivity back and cut down on distractions? Consider the source of your distractions. Your cell phone? Put it on silent, or better yet, turn it off and put it in a drawer. Out of sight and out of mind. Make sure you cannot hear any notification sounds, whether it’s a little ding or jingle or a vibration. This is crucial. Why? You may not realize it, but you’ve been trained to respond to those sounds, much like a cat to a can opener.
What about the Internet in general? If you’re working on a project and you already have the materials or information you need, consider cutting yourself off. If you’re connected to a WiFi network, disconnect. If you’re hardwired, pull the Ethernet cord out from the back of your computer. It may sound like a drastic step, but it works.
If you work in a busy environment, where people are chattering, phones are ringing and the printer is printing away, see if you can’t track down a different workspace. Look for an empty office or meeting room (don’t forget to ask first, just in case someone has a meeting later), and close the door.
It’s all about being proactive in cutting down the distraction. There isn’t a foolproof way to eliminate them all, but a little adjusting can go a long way.
Virus of the Month
Parasitic viruses, also known as file viruses,
spread by attaching themselves to programs.
When you start a program infected with a parasitic virus, the virus code is run. To hide itself, the virus then passes control back to the original program.

The operating system on your computer sees the virus as part of the program you were trying to run and gives it the same rights. These rights allow the virus to copy itself, install in memory or make changes on your computer.
Parasitic viruses appeared early in virus history and then became quite rare. However, they are now becoming more common again with recent examples including Sality, Virut and Vetor.”
- “Data Theft.” Threatsaurus: the a-z of computer and data security threats. Boston: Sophos, 2009. 53. Print.
Shiny New Gadget Of The Month:
Sony Xperia Z3 Compact
very fall a batch of cool new phones from nearly every major manufacturer hits the market. People are clamoring for the new, larger Apple iPhone or the new Google Nexus phone. This October saw the release of a rather interesting new Android phone from Sony called the Xperia Z3 Compact. What makes Sony’s phone remarkable?
Have you noticed how big phones have gotten lately? Not only that, but these big phones require quite a bit of battery power. The Z3 Compact is a premium phone that returns to a more palm-friendly size, with a 4.6-inch display. It also boasts a battery that lasts two days (or more, in some cases) with average use. That’s basically unheard of anymore. It also runs the latest version of Android, and it’s water-resistant. That’s right! The Z3 Compact is certified water-resistant up to one meter for a total of 30 minutes.

Think through Social Media Actions In A Heated Moment
Think through Social Media Actions In A Heated Moment
- If you wouldn’t say it to your grandmother, don’t write it on Twitter. The oldest test in the book is the grandma test. It still holds today. If she would be appalled, odds are that others will be too. It feels good to blast an opponent, but such outburst can easily be used against you.
- Remember that everything you say or do on the web is archived. Even if the NSA happens to miss it, odds are that Twitter, Facebook, Google and/or other platforms have a way of archiving the information. Consider everything you write these days on the Internet to be permanent. Trolls may delete their comments but they still leave a trail.
- Still debating saying it? Sleep on it. This is familiar but often good advice. If you really feel the need to say something that might be taken the wrong way, consider sitting on it overnight. Waiting until the next day will rarely hurt your point, and it may save huge amounts of embarrassment.
- If you do say it… make sure you feel that you could defend it in a court of law. Falsely accusing someone of something is a big deal and the repercussions could amplify beyond your original intentions.
- Remember that your reputation is cumulative. How you respond to the unfair and uncivil will either enhance or detract from your reputation. Don’t let others bait you into ruining your reputation.
How do I react when I am targeted on social media?
- Grab screenshots. If someone truly is going after you, the first move is to gather evidence. Make sure you have copies. Odds are that they will quickly realize what they have done and will try to erase their trail, so the best thing you can do is make sure you have a copy on hand.
- Report them. Twitter, LinkedIn, Facebook and most other platforms have safeguards against those who harass others. Don’t hesitate to put in a report—that’s why it’s there!
- Try not to react. This goes back to my above points about guarding yourself. As hard as it is, try to remember that once integrity is lost it is extremely hard to recover. The more reaction, the more fuel you pour on the fire.
- Remember that the truth is the best defense. As someone who has been egregiously accused of something I did not do, I took solace in the fact that I was innocent and as such the accusation cruelly asserted could never be proven.
We live in a world where unscrupulous people have migrated to online communities and live among the rest of us. I hope you never have to use the above actions, but that when you do, I hope they serve you well.

Mark Sanborn, CSP, CPAE, is president of Sanborn & Associates, Inc., an idea studio dedicated to developing leaders in business and in life. Mark is an international best-selling author and noted authority on leadership, team-building, customer service and change. Mark is the author of 8 books, including the best seller The Fred Factor: How Passion in Your Work and Life Can Turn the Ordinary into the Extraordinary, which has sold more than 1.6 million copies internationally. Learn more about Mark at www.marksanborn.com
Simple Ways to Use E-mail More Efficiently
There used to be a time when e-mail was supposed to increase productivity. Yet, that is often not the case. Many users don’t use e-mail as productively as they could, and you may be one of them! Consider these tips to improve the way you use e-mail:
Skip attachments. Find alternate methods of sharing documents, such as Google Drive or Dropbox. It makes organization and collaboration more efficient, and it’s easier to track who has what. Plus, many e-mail clients, such as Gmail, are notorious for marking e-mails with attachments and links as spam.
Watch your replies. When you reply to an e-mail, it’s too easy to write and send, not realizing who might end up with your message. If you receive a CC’d e-mail with several names attached, be sure to reply only to the sender and not the group, unless it’s 100% relevant. It creates useless in-box clutter for others and wastes time.
Use the subject line effectively. When a subject line is vague or difficult to understand, it’s frustrating for the recipient. They might not even bother with it. Be clear and concise, while also being descriptive. The recipient should know what the e-mail pertains to before they open it.
Not everything needs a reply. Replying to every e-mail you get, or even a majority of them, wastes your time and the time of the recipient, especially if your reply doesn’t say anything meaningful (such as a thanks or acknowledgment of a previous e-mail). Unless it’s absolutely necessary to continue a conversation, move on.
The Lighter Side:
Glowing Clouds Above Los Angeles

Of course, anyone who has lived outside of a city or has gone camping knows what those strange clouds in the Los Angeles sky were. No glowing acid rain here—it was the Milky Way! They were seeing an incredible flowing band of stars, gas and dust stretching across the entire sky for the first time in their lives. When you see that band of stars, it’s clear why we call our galaxy the Milky Way. Many other cultures have their own names for it, including “The Way the Dog Ran Away” (Cherokee), “Ganges River of Heaven” (Hindi), “The Road to Santiago” (Spanish) and “Hay Merchants Way” (Arabic).



